
Resources Blog
Featured Post
A Better Way to Fight Cybercrime: The Consortium
Battling cybercrime in the financial services industry can be downright scary. Threat actors are continuously evolving new phishing or ransomware campaigns on banks and credit unions.
Relationships overcome technology supply constraints
Preview for the Resources Blog - ODP Business Solutions secured a multifunction printer for a healthcare provider through their strong relationships with vendors, even during a time when supply constraints throughout the industry made this issue almost impossible. Read more to find out how.
f23fe41ff42268d7aed4ff0000da3176.png?sfvrsn=e41d8cbe_1)
NCUA Released Capital Stress Test Scenarios. Now What?
NCUA stress test scenarios have been released. Covered credit unions are required to complete the modeling scenarios by May 31. Catalyst can help.

70% of Smaller Financial Institutions See Surge In Trending Fraud Attacks
Fraudsters are taking advantage of common activities such as refueling your car or withdrawing money from an ATM. These fraudulent attacks occur frequently and smaller financial institutions are particularly vulnerable. To prevent such attacks, it is important to stay informed about the latest trends in fraud and take proactive measures. Read on to learn more about some of the current fraudulent attacks and how to prevent them.

Getting Fintech Innovation to Market in Record Time
The financial industry is constantly on its toes, ready to innovate when new consumer, regulatory, or technology trends emerge. However, the ambition to be first to market comes with challenges that can hinder even the most innovative organizations. Time, talent, and investment dollars are all limited resources and not having enough of these can impede a company's ability to beat the competition to the market.
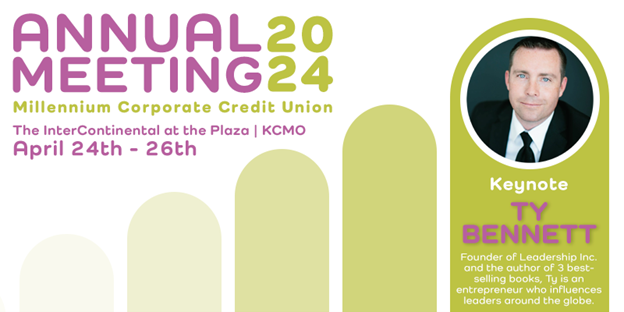
Ty Bennett to Keynote Millennium Corporate Credit Union 2024 Annual Meeting
Join Millennium Corporate, Ty Bennett, your credit union colleagues, and a team of talented speakers at the 2024 Annual Meeting in Kansas City!
Rethinking Overdraft Services for Your Credit Union to Remain Proactive
Evaluating your overdraft strategy is crucial, especially in light of the increased scrutiny and regulations to eliminate risky overdraft practices. The solution to this issue is straightforward: provide an overdraft service that is fully disclosed and has fair and reasonable fees. ADVANTAGE can assist you in achieving this goal.

NCUA issued an Advisory on Liquidity Risk Management
The NCUA issued an Advisory on Liquidity Risk Management. Here are four solutions that can help your credit union align with this advisory.
.png?sfvrsn=ef548bbe_3)
Real-Time Detection Solution Mitigates Check Fraud
In 2022 alone, financial institutions issued 680,000 reports of check fraud to the Financial Crimes Enforcement Network – an increase of 94% over the previous year. Lacking adequate security and detection controls can lead to significant financial loss.

Digital Loan Payment Process Solves Challenges
Adding a digital loan payment service can answer challenges credit union’s face. Here is a case study from a credit union in Texas that implemented Catalyst’s CU LoanPay solution.

Federal & State Labor Law Posters
As we prepare for 2024, one area of compliance often overlooked is labor law posters. Typically, the new year brings many legislative changes (minimum wage, paid leave, etc.) that employers are required to communicate to their workforce.
Subscribe
Sign up to the receive Cornerstone Resources blog notifications.
Need Solutions?
Cornerstone Resources offers a wide variety of products and services tailored to credit union interests.